A cipher takes a message (the plaintext) and encodes it --- puts it in a form (the ciphertext) where the information in the message is not obvious upon inspection. The recipient of the message takes the ciphertext and decodes it --- performs an operation which recovers the plaintext from the ciphertext.
Example. (A shift cipher) This is also known as a Caesar cipher, since it was supposedly used by Julius Caesar.
The letters of the alphabet will be represented by the numbers 0, ..., 25:
![]()
If x is a letter, I'll encode it using
![]()
(I could use any nonzero number from 1 to 25 in place of 11.) The formula above replaces each letter with another letter; in effect, the alphabet gets "shifted" 11 places to the left.
The translation table for this cipher is:
![]()
(a) Use this cipher to encrypt the message
![]()
(b) Find the decoding transformation for this cipher.
"I" is replaced by "T", "W" by "H", and so on. I get the ciphertext
![]()
I'll group the letters into 5-letter words to hide the original word groupings:
![]()
I've thrown in an extra "Z" at the end to make the last group come out evenly. If you decode the message, you'd get
![]()
You can see that the 5-letters grouping and the extra "Z"
did no harm, since it's evident what the plaintext was.![]()
(a) Solve the equation ![]() x:
x:
![]()
This equation is the decoding transformation; it's equivalent to
reading the translation table backward.![]()
Example. Consider the shift cipher
![]()
Use it to encrypt the message "I MUST HAVE FOOD".
The encrypted message is "B\ FNLM\ ATOX\ YHHW".
I wrote a computer program to do this. There are only 26 possible
shifts, so if you wanted to decode this by brute force, you could
feed the ciphertext through 26 shift programs and see which one
produced a sensible message. Shift ciphers are not of much use when
it comes to protecting secrets!![]()
The next thing to try is an affine transformation:
![]()
I need the last condition in order to ensure that I can decode
messages. This is equivalent to being able to invert the
transformation. Now if ![]() , then a is
invertible mod 26, so
, then a is
invertible mod 26, so
![]()
This equation can be used to decode messages.
Example. Consider the transformation ![]() .
.
(a) Encrypt the plaintext "WHEN WILL I BECOME A FISH".
(b) Find the decoding transformation.
(a) Here's the translation table:
![]()
The ciphertext is "UXIB\ UCRR\ C\ TIYGWI\ O\ NCAX".![]()
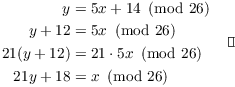
(b) Solve for x in terms of y:
Example. Consider the following affine cipher:
![]()
Find two plaintexts (input letters) that produce the same ciphertext (output letter).
I can produce two inputs that give the same output by finding two
inputs that make "![]() " equal to 0 mod
26. One such value is 0; I can produce another by using 13, since
" equal to 0 mod
26. One such value is 0; I can produce another by using 13, since
![]() .
.
![]()
The inputs are ![]() (which is "A") and
(which is "A") and
![]() (which is "N").
(which is "N").![]()
This isn't a very good affine cipher, since you can't construct a decoding transformation.
Shift ciphers and affine transformation ciphers are called substitution or character ciphers because each letter is replaced by another letter. They're simple to use, but relatively easy to crack. For example, with any reasonably large message you can count the letters in the ciphertext and guess the substitution using frequency tables for letters in the English language.
As a partial remedy to frequency analysis, you might think of
enciphering blocks of k letters at a time. To do this, encode letters
as number from 0 to 25 in the usual way. Consider a block of k
letters ![]() . As the cipher key,
choose a
. As the cipher key,
choose a ![]() matrix M which is invertible
mod 26. (M will be invertible mod 26 if
matrix M which is invertible
mod 26. (M will be invertible mod 26 if ![]() is relatively prime to 26.) Then the cipher
transformation is
is relatively prime to 26.) Then the cipher
transformation is ![]() , i.e.
, i.e.
![$$\left[\matrix{c_1 \cr c_2 \cr \vdots \cr c_k \cr}\right] = M \left[\matrix{a_1 \cr a_2 \cr \vdots \cr a_k \cr}\right] \mod{26}.$$](character-and-block-ciphers27.png)
You can decipher messages using ![]() .
.
Example. (a digraphic cipher) Consider the cipher
![]()
(a) Encode the message "SPICY MEATBALLS".
(b) Find the decoding transformation.
(a) Break the message up into two-letter groups and convert them to 2-dimensional vectors:
![]()
Finally, use M to encode each vector. For example,
![]()
![]() , so the first two
letters of the ciphertext are "FD".
, so the first two
letters of the ciphertext are "FD".
Continuing in this way, you obtain the ciphertext
![]()
(b) Let
![]()
Since ![]() and
and ![]() , M is invertible mod 26. In fact,
, M is invertible mod 26. In fact,
![]()
(Note that ![]() , because
, because ![]() .)
.)
The decoding transformation is
![]()
Example. Consider the following block cipher:
![]()
Find two different inputs ![]() and
and ![]() which produce the same output.
which produce the same output.
I'll find two different inputs which produce the same output ![]() . One such input is
. One such input is ![]() .
.
To find another, do the matrix multiplication and write out the two equations:
![]()
I can get a (nonzero) solution to the first equation by "switching and negating":
![]()
I try ![]() in the second equation:
in the second equation:
![]()
I didn't get 0, but since 22 has a factor of 2, I can get 0 by multiplying everything by 13:
![]()
This still satisfies ![]() .
.
Thus, ![]() and
and ![]() are two inputs which give the same output.
This shows that this block cipher is a poor cipher, since you won't
be able to construct a decoding transformation.
are two inputs which give the same output.
This shows that this block cipher is a poor cipher, since you won't
be able to construct a decoding transformation.![]()
Copyright 2019 by Bruce Ikenaga